We’ve reached an uncanny milestone in tech. We are building intimate conversational bonds with AI chatbots, yet the software infrastructure surrounding our daily lives remains as rigid, silent, and fragile as ever.
LLMs tease us with their facilities to write code, but forcing this new form of intelligence to work with programming paradigms that pre-date the World Wide Web is driving a silent crisis of structural decay in large-scale software systems.
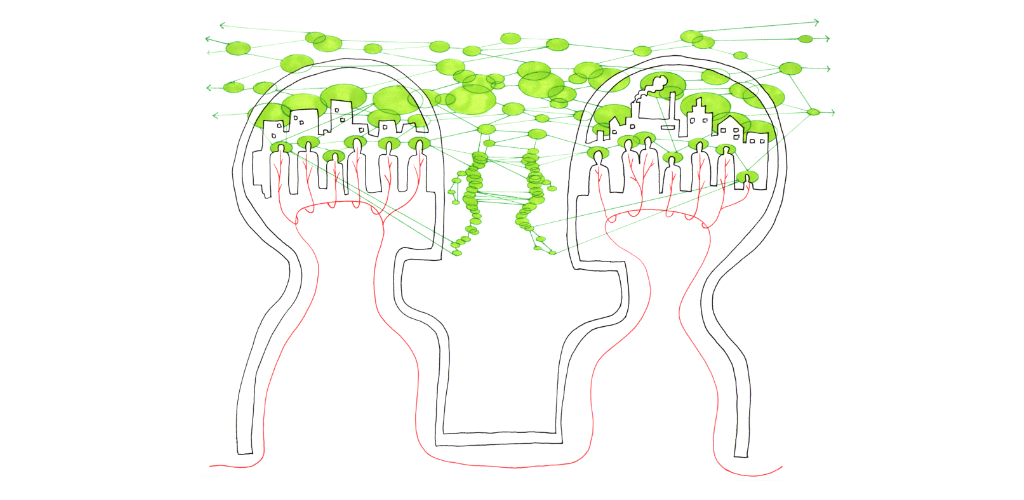
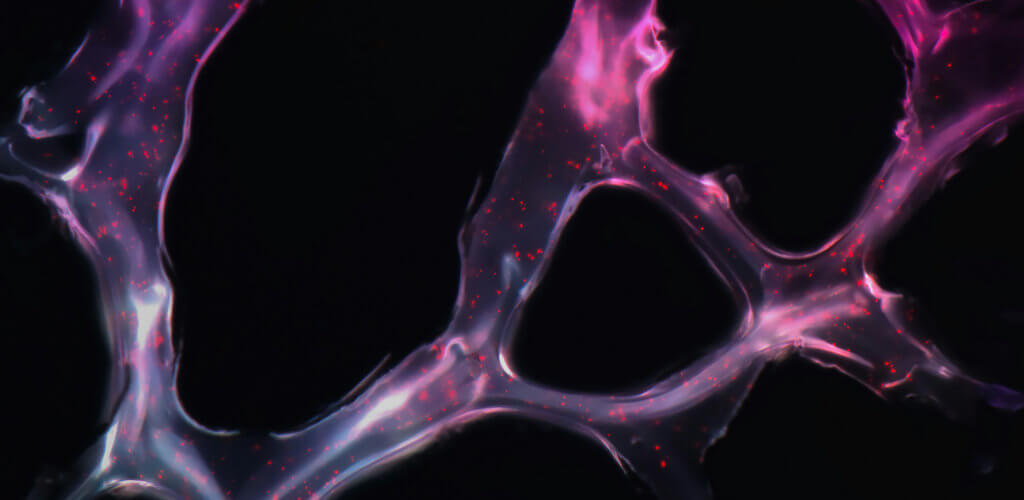
This post introduces the Software 4.0 era. Informed by biological processes, it turns software into a living, self-verifying organism that provides the perfect complement to LLMs. It transforms how we build and co-evolve the digital fabric of our world.
Read more